Mature and successful organisations have proven that they have done something right in the PAST. They may have been lucky to be in the right industry at the right time with the product and the business model that worked.
Can we expect that good business results in the past are a guarantee for the pole position in the future?
Financial Audit industry has evolved around this dilemma and is providing some assurance that financial statements can be trusted. Annual reports and quarterly disclosures can provide additional information to relevant stakeholders or public.
Regulated industries and listed companies are under increased scrutiny year by year as the world is trying to ensure investor confidence and trust in financial markets.
Still, not all tough questions are answered in those disclosures and annual reports. Why not?
There are many reasons and answers specific to individual organisation and case, however we can identify at least one common denominator – organisations are safeguarding some information – to preserve value.
A deep dive in organisation’s internal affairs is normal during the “mating process” – due diligence review.
If the financial, tax and compliance due diligence were the most important sources of information for setting the price for the company in the past, companies today are very dependent on their digital maturity.
It is critical to understand and assess ICT and digital business model maturity.
Big and regulated organisations:
Yes, it is true that some of that information comes from the internal audit reports, however internal audit functions are in many cases understaffed, and they are not seen as robust business advisors but rather as internal control specialists that were not exposed to many other environments. Most of small organisations and start-ups do not have internal audit functions.
True business advisor or consultant is in the position to bring value because of the regular and frequent exposure to various environments, industries, geographies, methodologies, research and at the end many good and not so good practices as well.
In many cases we complement internal audit functions by performing specific assurance or independent advisory tasks within and under the umbrella of the internal audit function. We firmly believe that organisations that take this co-sourcing approach are better positioned to identify unused potential and improve the maturity of the ICT and digital business models.
Small and Medium Enterprises:
How to assess small and medium sized organizations ICT and digital business model maturity?
SMEs may become potential new unicorns or investor nightmares. Level of uncertainty is even higher since most of SMEs and start-ups do not have internal audit functions.
We provide independent professional services for SMEs usually by initial diagnostic reviews. We assess the maturity of domains:
- Digital business models value.
Detailed due diligence reviews can go down to the level of details where we bring in if needed, specific technology or industry experts to perform deep dive assessments.
We help our clients to:
Better understand existing maturity of the ICT and digital business model maturity, risks, gaps and potential value;
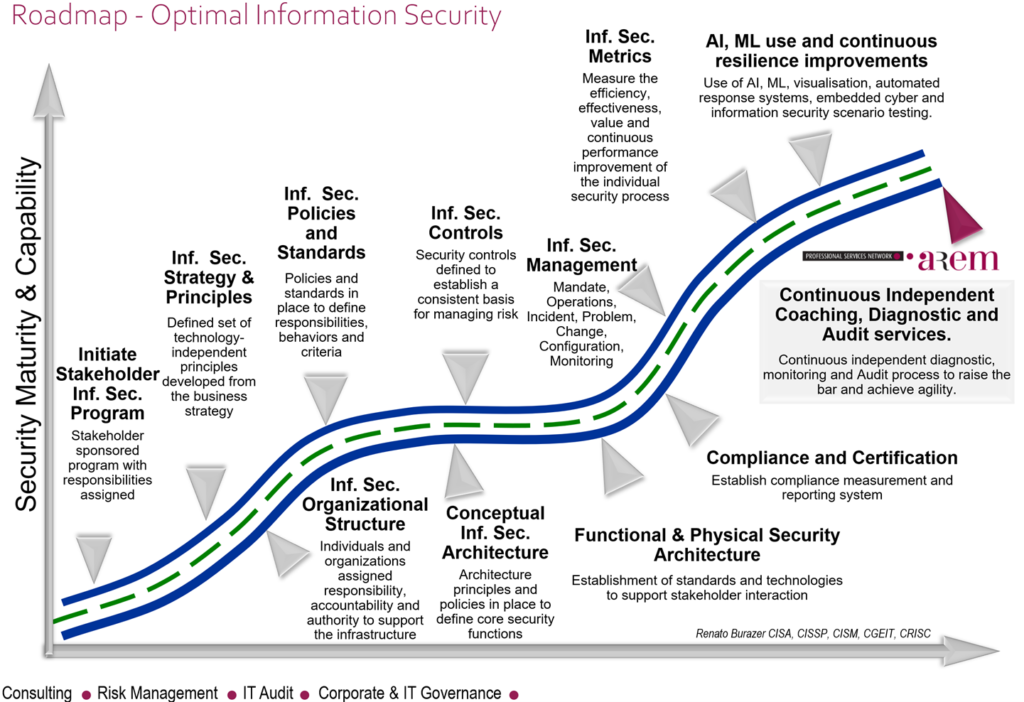
Develop vision and strategy for the ICT and digital business models;
Anticipate and resolve obstacles in the maturity improvement journey by: coaching, providing independent quality assurance support, or executing specific deep dive project tasks to help the projects remain on critical path.