Business, Governments and individuals – we are all reminded daily of our dependence on information.
We must protect the value of some information because we classified it as Confidential and we allow only trusted parties to access it. In this case we focus on Confidentiality.
We must protect some information from unwanted or undetected change to ensure its Integrity because corrupt or changed information could result in risk or loss in business terms or even loss of life in health care environments.
We want to ensure information is available to us when we need it. In this case we focus on Availability. Organizations have Business Continuity and Disaster Recovery Plans in place and they have prepared them by doing Business Impact Assessment (BIA) where they assess their business needs via Recovery Time Objective (RTO) and Recovery Point Objective (RPO).
As noted above CIA – Confidentiality, Integrity and Availability are important attributes of information that we are typically using to address information security needs.
All of the above is more or less clear to information security professionals and even general public, however, there are still significant differences in maturity of organizations when implementing Information Security Governance and Enterprise Risk Management.
These are some of our recent observations from working on Information Security or Risk Management consulting and Audit engagements:
How can we protect or secure something if we don’t even know what Information Assets we have, where they are and how important they are for the organization.
- Vulnerability management is slow and not efficient.
- Still there are unsupported and obsolete systems in use which are known to pose a risk because they have known vulnerabilities.
- Organizations are engaging managed security services providers, however, they are not always able to control their quality and performance.
- System Admins have many tools and control mechanisms at their disposal, however, they do not have the time or knowledge to implement them.
- There is high pressure from information security software and systems vendors on organizations as well as rapidly changing value propositions, licensing options and business models. Without robust IT Strategy and regular IT Architecture Scenario analysis it is very likely that vendors will have an upper hand.
- Only some organizations are executing all Cyber Security Scenarios beyond tabletop walkthrough exercises.
- Exit strategies are addressed formally (in regulated environments only) before entering into agreement as part of the risk assessment process, however, exit strategies are mostly forgotten and not tested during the course of cooperation.
This was just a sample we wanted to share but the list goes on and on.
So where do we go from here?
Every organization is unique, however, there are common Enterprise Risk and Information Security denominators related to Governance and Management. We didn’t comment on Enterprise Risk Management above, however, it is linked to Information Security.
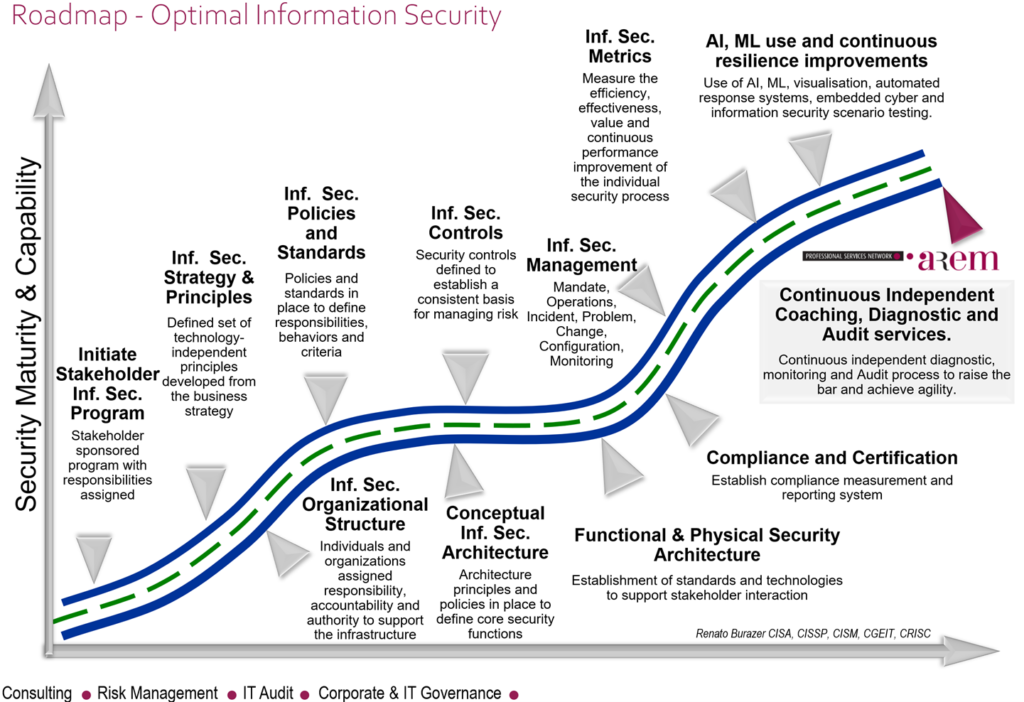
We will be happy to help you diagnose and improve the maturity of your Enterprise Risk and Information Security efforts or work with you on continuously raising the bar on the never ending journey to resilient, sustainable and agile organisation.
